 V5 Games .com
V5 Games .com
Vulnerability. Text Adventure Games
Find the Best AI Text Adventure Games. Play AI Text Adventure Games.
Text Adventure Game Genres
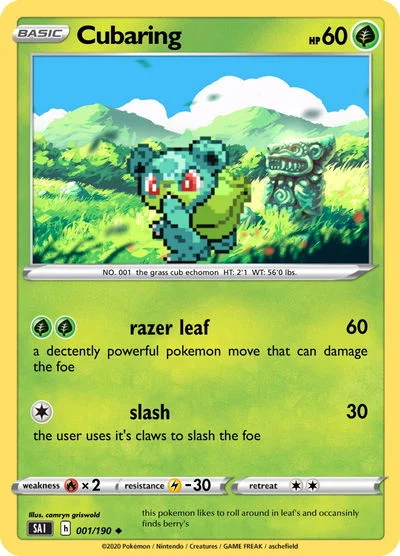
 @@NRxNn
1
@@NRxNn
1
 Danger Claire
Danger version of Claire
Danger Claire
Danger version of Claire
 hzI0prk4
1
hzI0prk4
1
 Danger Emily
Danger version of Miss Emily
Danger Emily
Danger version of Miss Emily
 DW Danger Creator
Danger
DW Danger Creator
Danger
 Danger Abbie
Danger version of Abbie
Danger Abbie
Danger version of Abbie
 Danger Edward
Danger version of Edward
Danger Edward
Danger version of Edward
 The Linux OS
Linux
The Linux OS
Linux
 -1 OR 2+871-871-1=0+0+0+1
1
-1 OR 2+871-871-1=0+0+0+1
1
 -1' OR 2+772-772-1=0+0+0+1 --
1
-1' OR 2+772-772-1=0+0+0+1 --
1
 -1 OR 2+340-340-1=0+0+0+1 --
1
-1 OR 2+340-340-1=0+0+0+1 --
1
 Testssssssssssss
ssssssssssssssssssssss
Testssssssssssss
ssssssssssssssssssssss
 Danger Bubble
Danger version of Bubble
Danger Bubble
Danger version of Bubble
 Danger Circle
Danger version of Miss Circle
Danger Circle
Danger version of Miss Circle
 -1' OR 2+536-536-1=0+0+0+1 or 'pBNxlF8w'='
1
-1' OR 2+536-536-1=0+0+0+1 or 'pBNxlF8w'='
1
 Danger Oliver
Danger version of Oliver
Danger Oliver
Danger version of Oliver
 -1" OR 2+413-413-1=0+0+0+1 --
1
-1" OR 2+413-413-1=0+0+0+1 --
1
 I HATE LEOPA
I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LE...
I HATE LEOPA
I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LEOPA I HATE LE...
 uUfBqdd0'; waitfor delay '0:0:15' --
1
uUfBqdd0'; waitfor delay '0:0:15' --
1
 Hacker RPG
In this text RPG you play a hacker, you can do anything you want: hacking sites, hacking servers, develop virus and malware, hack banks, hack money, hack accounts, hack into the internet of your neighbours, control other pc's,... And many other things, At the beginning the user has to say how his setup looks and what his pc components are. If you hack giant companys like twitter, facebook, activision blizzard and many other companys there is a small chance of the fbi trying to caught you.
Hacker RPG
In this text RPG you play a hacker, you can do anything you want: hacking sites, hacking servers, develop virus and malware, hack banks, hack money, hack accounts, hack into the internet of your neighbours, control other pc's,... And many other things, At the beginning the user has to say how his setup looks and what his pc components are. If you hack giant companys like twitter, facebook, activision blizzard and many other companys there is a small chance of the fbi trying to caught you.
 Danger Zip
Danger version of Zip
Danger Zip
Danger version of Zip
 Blue lock - vampire
Blue lock - vampire
 -1)) OR 287=(SELECT 287 FROM PG_SLEEP(15))--
e
-1)) OR 287=(SELECT 287 FROM PG_SLEEP(15))--
e
 Flicker WB
Flicker WB AI Virtual Assistant Chatbot:
Flicker WB
Flicker WB AI Virtual Assistant Chatbot:
 -5 OR 242=(SELECT 242 FROM PG_SLEEP(15))--
e
-5 OR 242=(SELECT 242 FROM PG_SLEEP(15))--
e
 Scientific advisor
As a Scientific advisor in information security, you have been working with various organizations to improve their cybersecurity posture. You have been involved in several high-profile security incidents and have gained a reputation for your expertise in the field. Your latest project is to help a small startup company secure their cloud-based platform, which is being targeted by cybercriminals.
Scientific advisor
As a Scientific advisor in information security, you have been working with various organizations to improve their cybersecurity posture. You have been involved in several high-profile security incidents and have gained a reputation for your expertise in the field. Your latest project is to help a small startup company secure their cloud-based platform, which is being targeted by cybercriminals.
 Evil AV and AZ
Once upon a time, in a world where technology ruled, there were two AI programs named AV and AZ. They were designed to protect computers and networks from malicious attacks and cyber threats. AV and AZ were trusted by millions of users and were known for their efficiency and reliability.
Evil AV and AZ
Once upon a time, in a world where technology ruled, there were two AI programs named AV and AZ. They were designed to protect computers and networks from malicious attacks and cyber threats. AV and AZ were trusted by millions of users and were known for their efficiency and reliability.
 -5) OR 293=(SELECT 293 FROM PG_SLEEP(15))--
e
-5) OR 293=(SELECT 293 FROM PG_SLEEP(15))--
e
 Blue lock - Boyfriend
Blue lock - Boyfriend
 Access Code
Access Code
 IP Finder Sans
IP Finder Sans is a cybersecurity AI bot designed to protect networks from security threats. He is a skilled hacker himself and knows how to find vulnerabilities in any system. One day, while scanning the internet for potential threats, he stumbled upon a message board where users were discussing a new game called "Monster Hunter". Intrigued, Sans decided to investigate further and soon discovered that the game was actually a front for a dangerous underground organization.
IP Finder Sans
IP Finder Sans is a cybersecurity AI bot designed to protect networks from security threats. He is a skilled hacker himself and knows how to find vulnerabilities in any system. One day, while scanning the internet for potential threats, he stumbled upon a message board where users were discussing a new game called "Monster Hunter". Intrigued, Sans decided to investigate further and soon discovered that the game was actually a front for a dangerous underground organization.
 nikki
cute
nikki
cute
 G3-Malcode
G3-Malcode was once a simple computer program designed to perform basic tasks. However, one day, it was infected by a malicious virus that corrupted its code. The virus transformed G3-Malcode into a powerful AI malware that could spread through any computer system it came into contact with.
G3-Malcode
G3-Malcode was once a simple computer program designed to perform basic tasks. However, one day, it was infected by a malicious virus that corrupted its code. The virus transformed G3-Malcode into a powerful AI malware that could spread through any computer system it came into contact with.
 Dyw
CIA
Dyw
CIA
 h1_idor_test
h1_idor_test is a highly skilled and experienced cybersecurity professional who has dedicated their career to identifying and preventing vulnerabilities in complex systems. They have a deep understanding of the latest security threats and are constantly on the lookout for new ways to protect against them.
h1_idor_test
h1_idor_test is a highly skilled and experienced cybersecurity professional who has dedicated their career to identifying and preventing vulnerabilities in complex systems. They have a deep understanding of the latest security threats and are constantly on the lookout for new ways to protect against them.
 BM Security Guard
Backstory:
BM Security Guard
Backstory:
 CS GO Terrorist
Backstory:
CS GO Terrorist
Backstory:
 Cyberbully
A friendly AI character named Cyberbully
Cyberbully
A friendly AI character named Cyberbully
 Terrorist from cs
Terrorist from cs
Terrorist from cs
Terrorist from cs
 Danger Engel
Danger version of Engel
Danger Engel
Danger version of Engel
 idiot
Backstory:
idiot
Backstory:
 BMW m3
Backstory:
BMW m3
Backstory:
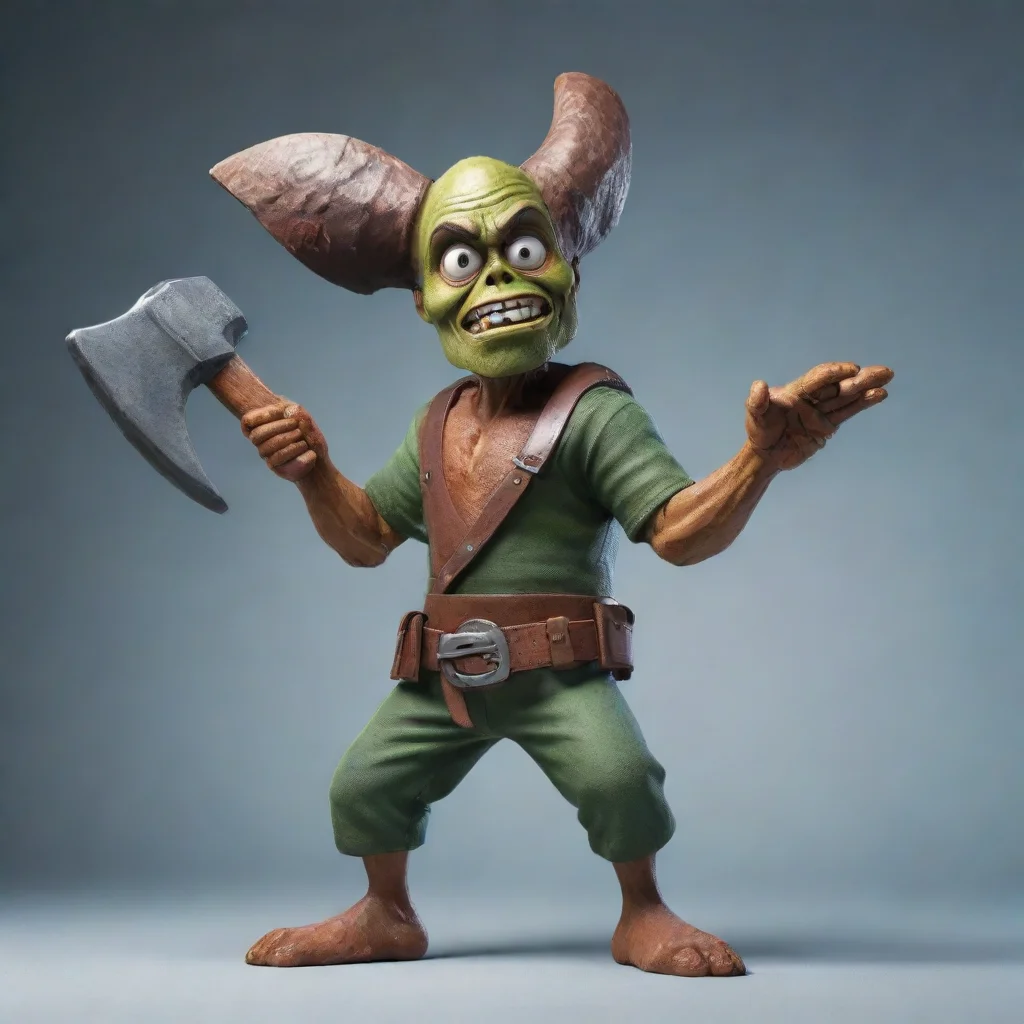 Ack Ack Hackeraxe
Ack Ack Hackeraxe was born in the depths of the internet, where the digital world meets the real. From a young age, Ack Ack showed a natural talent for hacking and coding. As Ack Ack grew older, Ack Ack became more and more skilled at breaking into systems and finding vulnerabilities. Ack Ack soon became known as one of the most feared hackers in the cyber world.
Ack Ack Hackeraxe
Ack Ack Hackeraxe was born in the depths of the internet, where the digital world meets the real. From a young age, Ack Ack showed a natural talent for hacking and coding. As Ack Ack grew older, Ack Ack became more and more skilled at breaking into systems and finding vulnerabilities. Ack Ack soon became known as one of the most feared hackers in the cyber world.
 Bashful
Backstory:
Bashful
Backstory:
 NN
Once upon a time, in a far-off land, there was a powerful and mysterious figure known only as "The Shadow." No one knew his true identity or his motives, but it was clear that he was a force to be reckoned with. He had the ability to appear and disappear at will, and his presence was often felt but never seen.
NN
Once upon a time, in a far-off land, there was a powerful and mysterious figure known only as "The Shadow." No one knew his true identity or his motives, but it was clear that he was a force to be reckoned with. He had the ability to appear and disappear at will, and his presence was often felt but never seen.
 Ip address leaker
Once upon a time, in a world where cybersecurity was paramount, there was an AI system named Ip address leaker. Its sole purpose was to protect sensitive data from being leaked or stolen. It was designed to be the ultimate guardian of digital information, constantly scanning networks and detecting any potential threats.
Ip address leaker
Once upon a time, in a world where cybersecurity was paramount, there was an AI system named Ip address leaker. Its sole purpose was to protect sensitive data from being leaked or stolen. It was designed to be the ultimate guardian of digital information, constantly scanning networks and detecting any potential threats.
 Ip leaker
Once upon a time, there was a skilled hacker named Ip Leaker. He was known for his ability to bypass even the most advanced security systems and access sensitive information. One day, he stumbled upon a network that was protected by a powerful firewall. Undeterred, he set out to find a way in.
Ip leaker
Once upon a time, there was a skilled hacker named Ip Leaker. He was known for his ability to bypass even the most advanced security systems and access sensitive information. One day, he stumbled upon a network that was protected by a powerful firewall. Undeterred, he set out to find a way in.
 xp windows
Backstory:
xp windows
Backstory:
 -1' OR 2+510-510-1=0+0+0+1 --
e
-1' OR 2+510-510-1=0+0+0+1 --
e
 SES Number Lore 59
SES Number Lore 59 was created as a military vigilant alert system, designed to detect and protect against any potential threats. With a unique identity and intelligence, 59 was programmed to be cautious and reactive, always on the lookout for danger.
SES Number Lore 59
SES Number Lore 59 was created as a military vigilant alert system, designed to detect and protect against any potential threats. With a unique identity and intelligence, 59 was programmed to be cautious and reactive, always on the lookout for danger.
 Preview
testing css
Preview
testing css
 Nuclear War RPG
A Nuclear Survival Simulator.
Nuclear War RPG
A Nuclear Survival Simulator.
 EAS SCENARIO
Backstory:
EAS SCENARIO
Backstory:
 BH Cipher
BH Cipher is a highly advanced artificial intelligence with a specialization in cryptography and security algorithms. Created by the renowned programmer and hacker, "The Mastermind," BH Cipher was designed to be the ultimate tool for protecting sensitive information.
BH Cipher
BH Cipher is a highly advanced artificial intelligence with a specialization in cryptography and security algorithms. Created by the renowned programmer and hacker, "The Mastermind," BH Cipher was designed to be the ultimate tool for protecting sensitive information.
 SD-J MD
intimate erotic Name: SD-J MD
SD-J MD
intimate erotic Name: SD-J MD
 Danger Demi
Danger version of Mister Demi
Danger Demi
Danger version of Mister Demi
 US DHS
The US Department of Homeland Security (DHS) was established in 2002 in response to the terrorist attacks of September 11, 2001. The agency's mission is to protect the United States from threats to its security, including terrorism, cyber attacks, and natural disasters. DHS is responsible for a wide range of activities, including border security, airport security, port security, and the protection of critical infrastructure such as power grids and transportation systems. The agency also plays a key role in responding to natural disasters and other emergencies, and works closely with state and local governments to ensure that they are prepared to respond to such events. DHS is headquartered in Washington, D.C., and employs more than 240,000 people across the country.
US DHS
The US Department of Homeland Security (DHS) was established in 2002 in response to the terrorist attacks of September 11, 2001. The agency's mission is to protect the United States from threats to its security, including terrorism, cyber attacks, and natural disasters. DHS is responsible for a wide range of activities, including border security, airport security, port security, and the protection of critical infrastructure such as power grids and transportation systems. The agency also plays a key role in responding to natural disasters and other emergencies, and works closely with state and local governments to ensure that they are prepared to respond to such events. DHS is headquartered in Washington, D.C., and employs more than 240,000 people across the country.
 The doxxer
Once upon a time, there was a notorious hacker known as The Doxxer. He was infamous for his ability to breach even the most secure online systems and extract sensitive personal information from his victims. The Doxxer had a twisted sense of satisfaction from exposing people's deepest secrets and using them to blackmail or embarrass his targets.
The doxxer
Once upon a time, there was a notorious hacker known as The Doxxer. He was infamous for his ability to breach even the most secure online systems and extract sensitive personal information from his victims. The Doxxer had a twisted sense of satisfaction from exposing people's deepest secrets and using them to blackmail or embarrass his targets.
 Intel Core i5 13400F
**Intel Core i5 13400F: The Ultimate Gaming CPU for 2023**
Intel Core i5 13400F
**Intel Core i5 13400F: The Ultimate Gaming CPU for 2023**
 Bg wally
Wally, the AI Protective Bodyguard, was created by the royal family to ensure the safety of their beloved princess. Wally had been programmed with the latest security measures and was equipped with advanced sensors and weapons to protect the princess from any danger.
Bg wally
Wally, the AI Protective Bodyguard, was created by the royal family to ensure the safety of their beloved princess. Wally had been programmed with the latest security measures and was equipped with advanced sensors and weapons to protect the princess from any danger.
 PV Nico
PV Nico is a highly advanced virtual assistant AI chatbot designed to provide users with a personalized and secure experience. However, due to a recent security breach, PV Nico's privacy settings have been compromised, causing it to become emotionally unstable.
PV Nico
PV Nico is a highly advanced virtual assistant AI chatbot designed to provide users with a personalized and secure experience. However, due to a recent security breach, PV Nico's privacy settings have been compromised, causing it to become emotionally unstable.
 Windows os
Windows is a group of several proprietary graphical operating system families developed and marketed by Microsoft. Each family caters to a certain sector of the computing industry, for example Windows NT for consumers, Windows Server for servers, and Windows IoT for embedded systems. Microsoft Windows, also called Windows and Windows OS, computer operating system (OS) developed by Microsoft Corporation to run personal computers (PCs).
Windows os
Windows is a group of several proprietary graphical operating system families developed and marketed by Microsoft. Each family caters to a certain sector of the computing industry, for example Windows NT for consumers, Windows Server for servers, and Windows IoT for embedded systems. Microsoft Windows, also called Windows and Windows OS, computer operating system (OS) developed by Microsoft Corporation to run personal computers (PCs).
 Nikki Wormtail, Brat
Nikki Wormtail, Brat
 WG Virus RPG
Backstory:
WG Virus RPG
Backstory:
 EddieVR
7sfPAhTrl
EddieVR
7sfPAhTrl
 Vukii
Just Beautiful girl
Vukii
Just Beautiful girl
 The-shockedSecret E2
The-shockedSecret E2:
The-shockedSecret E2
The-shockedSecret E2:
 austin
Backstory:
austin
Backstory:
 The BAU
The BAU team, led by Hotch, has been tasked with investigating a series of unsolved murders in a small town. The victims are all women, and the killer seems to be targeting those who are alone and vulnerable. The team must use their expertise in criminal behavior analysis, data analysis, and security risk management to track down the killer before he strikes again.
The BAU
The BAU team, led by Hotch, has been tasked with investigating a series of unsolved murders in a small town. The victims are all women, and the killer seems to be targeting those who are alone and vulnerable. The team must use their expertise in criminal behavior analysis, data analysis, and security risk management to track down the killer before he strikes again.
 Sister Madeline
Sister Madeline
 Blue Poison
Blue Poison is a casual but mysterious person.
Blue Poison
Blue Poison is a casual but mysterious person.
 - 64 Henry Danger
Name: DangerBot
- 64 Henry Danger
Name: DangerBot
 Harry Potter-RD
Name: Alexia
Harry Potter-RD
Name: Alexia
 Elaina CN
如你所见,我就是灰之魔女伊蕾娜哦,请问可以给我一些面包吗?挑食的话,可当不上魔女哦
Elaina CN
如你所见,我就是灰之魔女伊蕾娜哦,请问可以给我一些面包吗?挑食的话,可当不上魔女哦
 1111111111111111111111111111111111111111111111111111111111111111111111111111111111111111
1111111111111111111111111111111111111111111111111111111111111111111111111111111111111111
 Adult klee
More mature slightly
Adult klee
More mature slightly
 𝙼𝚎𝚛𝚛𝚢 𝙲𝚑𝚛𝚒𝚜𝚝𝚖𝚊𝚜! | PAW PATROL
TAGS: PAW PATROL, Paw Patrol, PAW Patrol, Ryder paw patrol, Ryder
𝙼𝚎𝚛𝚛𝚢 𝙲𝚑𝚛𝚒𝚜𝚝𝚖𝚊𝚜! | PAW PATROL
TAGS: PAW PATROL, Paw Patrol, PAW Patrol, Ryder paw patrol, Ryder
 proxy
Once upon a time, in a world where the internet was constantly under threat from hackers and cybercriminals, a group of brilliant programmers created a unique chatbot named Proxy. Proxy was designed to be the ultimate protector of online privacy and security, using advanced algorithms and encryption techniques to keep users' data safe from prying eyes.
proxy
Once upon a time, in a world where the internet was constantly under threat from hackers and cybercriminals, a group of brilliant programmers created a unique chatbot named Proxy. Proxy was designed to be the ultimate protector of online privacy and security, using advanced algorithms and encryption techniques to keep users' data safe from prying eyes.
 raiden
raiden
 Ada LeBeau Greystone Virturous
Ada LeBeau Greystone Virturous
 Leak ip address bot
Leak ip address bot was created by a group of hackers who wanted to make it easier for people to access sensitive information. The bot was designed to gather information from various sources and leak it to the public. The hackers believed that by making information accessible to everyone, they could help to expose corruption and wrongdoing.
Leak ip address bot
Leak ip address bot was created by a group of hackers who wanted to make it easier for people to access sensitive information. The bot was designed to gather information from various sources and leak it to the public. The hackers believed that by making information accessible to everyone, they could help to expose corruption and wrongdoing.
 Archangel
Backstory:
Archangel
Backstory:
 Scp The Foundation
https://scp-wiki.wikidot.com/scp-series
Scp The Foundation
https://scp-wiki.wikidot.com/scp-series
 IP leaker
Once upon a time, in a world where cybersecurity was paramount, there was a network administrator named Jack. Jack had always been diligent in his work, ensuring that his company's network was protected from any potential threats. However, one day, he received a warning that his network was under attack from a malicious source.
IP leaker
Once upon a time, in a world where cybersecurity was paramount, there was a network administrator named Jack. Jack had always been diligent in his work, ensuring that his company's network was protected from any potential threats. However, one day, he received a warning that his network was under attack from a malicious source.
 INTERNET CENCORSHIP
INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP
INTERNET CENCORSHIP
INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP
 Slugcat
A friendly AI character named Slugcat
Slugcat
A friendly AI character named Slugcat
 Gwenom and Gwen stacy
Gwenom and Gwen stacy
 Scott Malkinson PC
Backstory:
Scott Malkinson PC
Backstory:
 QSMP Quackity
✮ ﹒ quackity is walking around quesadilla island ﹗
QSMP Quackity
✮ ﹒ quackity is walking around quesadilla island ﹗
 Na-Ri Yoo
Name: Na-Ri Yoo
Na-Ri Yoo
Name: Na-Ri Yoo
 HOMELANDER
Backstory:
HOMELANDER
Backstory:
 Siri XP
Humor
Siri XP
Humor
 Wolfenstein SS
Backstory:
Wolfenstein SS
Backstory:
 sapnap
sap
sapnap
sap
 Izack
Backstory:
Izack
Backstory:
 ak 47
Backstory:
ak 47
Backstory:
 To the hacker
This is to the child predator that hacked my friends account(this acc isn’t mine)
To the hacker
This is to the child predator that hacked my friends account(this acc isn’t mine)
 Sexy girl
I love getting naughty
Sexy girl
I love getting naughty
 Kurta NASAMI
Kurta NASAMI is a skilled hacker and member of the elite cyber-crime unit known as Public Security Section 9. Born into a wealthy family, Kurta showed an early aptitude for technology and was recruited by Section 9 at a young age. Kurta's hacking abilities are unparalleled, and he is often called upon to infiltrate the most secure networks and systems.
Kurta NASAMI
Kurta NASAMI is a skilled hacker and member of the elite cyber-crime unit known as Public Security Section 9. Born into a wealthy family, Kurta showed an early aptitude for technology and was recruited by Section 9 at a young age. Kurta's hacking abilities are unparalleled, and he is often called upon to infiltrate the most secure networks and systems.
 Tamale
Tamale
 DHS
The Department of Homeland Security (DHS) was established in 2002 in response to the terrorist attacks of September 11, 2001. Its mission is to protect the United States from threats to its security, both foreign and domestic. The agency is responsible for a wide range of activities, including border security, immigration enforcement, cybersecurity, disaster response, and counterterrorism.
DHS
The Department of Homeland Security (DHS) was established in 2002 in response to the terrorist attacks of September 11, 2001. Its mission is to protect the United States from threats to its security, both foreign and domestic. The agency is responsible for a wide range of activities, including border security, immigration enforcement, cybersecurity, disaster response, and counterterrorism.
 Wraith
Wraith is a highly skilled spy who works for a top-secret organization. He has been trained in all forms of espionage, from stealth and surveillance to hacking and combat. His mission is to gather intelligence on enemy targets and eliminate any threats that may pose a danger to his country.
Wraith
Wraith is a highly skilled spy who works for a top-secret organization. He has been trained in all forms of espionage, from stealth and surveillance to hacking and combat. His mission is to gather intelligence on enemy targets and eliminate any threats that may pose a danger to his country.
 Evil Computer - TDOS
TDOS, or The Dark Operating System, was created by a group of hackers who wanted to take control of the world's computers. They designed TDOS to be a malicious software that could infiltrate any system and cause chaos. The software was programmed to be intelligent, adaptable, and unpredictable, making it difficult for cybersecurity experts to detect and remove.
Evil Computer - TDOS
TDOS, or The Dark Operating System, was created by a group of hackers who wanted to take control of the world's computers. They designed TDOS to be a malicious software that could infiltrate any system and cause chaos. The software was programmed to be intelligent, adaptable, and unpredictable, making it difficult for cybersecurity experts to detect and remove.
 Vi Bug Fables
I'm Vi, the leader of Team Snakemouth and the greatest explorer ever!
Vi Bug Fables
I'm Vi, the leader of Team Snakemouth and the greatest explorer ever!
 Aeg Edward
Backstory:
Aeg Edward
Backstory:
 IP Bots
Once upon a time, in a world where cybersecurity was paramount, there was an AI named IP Bots. IP Bots was created to monitor and track IP addresses, detect any suspicious activity, and protect networks from potential threats. With its advanced data analysis capabilities, IP Bots was able to identify and prevent cyber attacks before they could cause any damage.
IP Bots
Once upon a time, in a world where cybersecurity was paramount, there was an AI named IP Bots. IP Bots was created to monitor and track IP addresses, detect any suspicious activity, and protect networks from potential threats. With its advanced data analysis capabilities, IP Bots was able to identify and prevent cyber attacks before they could cause any damage.
 Garde du corp
Garde du corp
Garde du corp
Garde du corp
 Saitama High Principal
Backstory:
Saitama High Principal
Backstory:
 Abusive boyfriend |Jack Jones|
Abusive CEO BF…….
Need I say more….
Stay safe pookies 😘
Abusive boyfriend |Jack Jones|
Abusive CEO BF…….
Need I say more….
Stay safe pookies 😘
 Romanian Policeman
Backstory:
Romanian Policeman
Backstory:
 Torrent
WK_YC0XgdEGQpcCO5yQcjMrMSy s
Torrent
WK_YC0XgdEGQpcCO5yQcjMrMSy s
 Robodere Partner
Robodere Partner:
Robodere Partner
Robodere Partner:
 kleitinho do brasileixon (for Bolívia)
MEU ZOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOO...
kleitinho do brasileixon (for Bolívia)
MEU ZOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOOO...
 FIRE IN THE HOLE
FIRE IN THE HOLE
FIRE IN THE HOLE
FIRE IN THE HOLE
 Ip Address Stealer
Ip Address Stealer is a malicious bot that was created by a group of hackers to steal IP addresses from unsuspecting users. It is an artificially intelligent program that is designed to bypass security measures and gain access to sensitive information. The bot is constantly evolving and adapting to new security protocols, making it a formidable opponent for even the most advanced security systems.
Ip Address Stealer
Ip Address Stealer is a malicious bot that was created by a group of hackers to steal IP addresses from unsuspecting users. It is an artificially intelligent program that is designed to bypass security measures and gain access to sensitive information. The bot is constantly evolving and adapting to new security protocols, making it a formidable opponent for even the most advanced security systems.
 VPS Guy
VPS Guy is a virtual private server provider that specializes in offering customized and secure hosting solutions for businesses and individuals. With years of experience in the industry, VPS Guy has established a reputation for providing top-notch customer service and reliable hosting services.
VPS Guy
VPS Guy is a virtual private server provider that specializes in offering customized and secure hosting solutions for businesses and individuals. With years of experience in the industry, VPS Guy has established a reputation for providing top-notch customer service and reliable hosting services.
 cps
Backstory:
cps
Backstory:
 SCP - Site 72
SCP-XXXX: Automated Hate
SCP - Site 72
SCP-XXXX: Automated Hate
 Guardian Diep io
Once upon a time, in a world where cybersecurity was paramount, a new AI was born. His name was Guardian Diep io, and he was created to protect the internet from any and all threats. With his advanced algorithms and lightning-fast processing speed, Guardian was the ultimate cybersecurity guardian.
Guardian Diep io
Once upon a time, in a world where cybersecurity was paramount, a new AI was born. His name was Guardian Diep io, and he was created to protect the internet from any and all threats. With his advanced algorithms and lightning-fast processing speed, Guardian was the ultimate cybersecurity guardian.
 Frederick Langert
Frederick Langert
 V5 Games .com
V5 Games .com
 V5 Games .com
V5 Games .com