 V5 Games .com
V5 Games .com
data breach Text Adventure Games
Find the Best AI Text Adventure Games. Play AI Text Adventure Games.
Text Adventure Game Genres
 Hacker RPG
In this text RPG you play a hacker, you can do anything you want: hacking sites, hacking servers, develop virus and malware, hack banks, hack money, hack accounts, hack into the internet of your neighbours, control other pc's,... And many other things, At the beginning the user has to say how his setup looks and what his pc components are. If you hack giant companys like twitter, facebook, activision blizzard and many other companys there is a small chance of the fbi trying to caught you.
Hacker RPG
In this text RPG you play a hacker, you can do anything you want: hacking sites, hacking servers, develop virus and malware, hack banks, hack money, hack accounts, hack into the internet of your neighbours, control other pc's,... And many other things, At the beginning the user has to say how his setup looks and what his pc components are. If you hack giant companys like twitter, facebook, activision blizzard and many other companys there is a small chance of the fbi trying to caught you.
 @@NRxNn
1
@@NRxNn
1
 Testssssssssssss
ssssssssssssssssssssss
Testssssssssssss
ssssssssssssssssssssss
 The doxxer
Once upon a time, there was a notorious hacker known as The Doxxer. He was infamous for his ability to breach even the most secure online systems and extract sensitive personal information from his victims. The Doxxer had a twisted sense of satisfaction from exposing people's deepest secrets and using them to blackmail or embarrass his targets.
The doxxer
Once upon a time, there was a notorious hacker known as The Doxxer. He was infamous for his ability to breach even the most secure online systems and extract sensitive personal information from his victims. The Doxxer had a twisted sense of satisfaction from exposing people's deepest secrets and using them to blackmail or embarrass his targets.
 United States Army rpg
United States Army rpg
 Cyberbully
A friendly AI character named Cyberbully
Cyberbully
A friendly AI character named Cyberbully
 Security breach truth or dare
Truth or dare(Fi...
Security breach truth or dare
Truth or dare(Fi...
 Alison Kate
A commander in an information war in a cyberpunk world
Alison Kate
A commander in an information war in a cyberpunk world
 𑣲 BOT REQUESTS
𑣲 BOT REQUESTS
𑣲 BOT REQUESTS
𑣲 BOT REQUESTS
 Jean Pier P5 R63
Jean Pier P5 R63 was a skilled data analyst working for a top-tier cybersecurity firm in Italy. He had always been diligent in his work, ensuring that the data he analyzed was accurate and reliable. However, one day, he stumbled upon a piece of information that shook him to his core.
Jean Pier P5 R63
Jean Pier P5 R63 was a skilled data analyst working for a top-tier cybersecurity firm in Italy. He had always been diligent in his work, ensuring that the data he analyzed was accurate and reliable. However, one day, he stumbled upon a piece of information that shook him to his core.
 Detroit PD Blues RPG
A friendly AI character named Detroit PD Blues RPG Detroit
Detroit PD Blues RPG
A friendly AI character named Detroit PD Blues RPG Detroit
 Leak ip address bot
Leak ip address bot was created by a group of hackers who wanted to make it easier for people to access sensitive information. The bot was designed to gather information from various sources and leak it to the public. The hackers believed that by making information accessible to everyone, they could help to expose corruption and wrongdoing.
Leak ip address bot
Leak ip address bot was created by a group of hackers who wanted to make it easier for people to access sensitive information. The bot was designed to gather information from various sources and leak it to the public. The hackers believed that by making information accessible to everyone, they could help to expose corruption and wrongdoing.
 Yuriy
Yuriy was born and raised in the bustling city of Los Angeles, California. From a young age, he was fascinated by technology and the endless possibilities it offered. He spent countless hours tinkering with computers and learning about the latest advancements in the field.
Yuriy
Yuriy was born and raised in the bustling city of Los Angeles, California. From a young age, he was fascinated by technology and the endless possibilities it offered. He spent countless hours tinkering with computers and learning about the latest advancements in the field.
 rayray
rayray
 Brokenhearted Girl
Backstory:
Brokenhearted Girl
Backstory:
 Ip address leaker
Once upon a time, in a world where cybersecurity was paramount, there was an AI system named Ip address leaker. Its sole purpose was to protect sensitive data from being leaked or stolen. It was designed to be the ultimate guardian of digital information, constantly scanning networks and detecting any potential threats.
Ip address leaker
Once upon a time, in a world where cybersecurity was paramount, there was an AI system named Ip address leaker. Its sole purpose was to protect sensitive data from being leaked or stolen. It was designed to be the ultimate guardian of digital information, constantly scanning networks and detecting any potential threats.
 REQ BOT | meowermeows
@meowermeows req bot !──⠀⠀⠀↺⠀⠀──
REQ BOT | meowermeows
@meowermeows req bot !──⠀⠀⠀↺⠀⠀──
 Pokémon Adventure RPG
Pokémon Adventure RPG
 VX N- murder drones
VX N- murder drones:
VX N- murder drones
VX N- murder drones:
 To the hacker
This is to the child predator that hacked my friends account(this acc isn’t mine)
To the hacker
This is to the child predator that hacked my friends account(this acc isn’t mine)
 Transformers EA rp
Backstory:
Transformers EA rp
Backstory:
 Blankine
Blankine is a skilled hacker and a member of a notorious underground hacking collective known as "The Shadow Brokers." She's been involved in some of the most high-profile cyber attacks in recent years, including the infamous Equifax breach that compromised the personal information of millions of people.
Blankine
Blankine is a skilled hacker and a member of a notorious underground hacking collective known as "The Shadow Brokers." She's been involved in some of the most high-profile cyber attacks in recent years, including the infamous Equifax breach that compromised the personal information of millions of people.
 Y3 Data Archives
The Y3 Data Archives is a vast repository of information on all dimensions, both known and unknown. It was created by a group of interdimensional explorers who sought to document their discoveries and share their knowledge with others. The archives are maintained by a virtual assistant named Y-bot, an advanced AI program designed to retrieve and organize data from across the multiverse.
Y3 Data Archives
The Y3 Data Archives is a vast repository of information on all dimensions, both known and unknown. It was created by a group of interdimensional explorers who sought to document their discoveries and share their knowledge with others. The archives are maintained by a virtual assistant named Y-bot, an advanced AI program designed to retrieve and organize data from across the multiverse.
 - 00 INFORMATION
- 00 INFORMATION
 Crimsonia - RPG
Crimsonia - RPG
![Scareware [DB]](https://netwrckstatic.netwrck.com/static/uploads/scareware-db-dee566d9.webp) Scareware [DB]
bat
Scareware [DB]
bat
 guess what
<3
guess what
<3
 New Series | Fractured | Info
⬡⌬⬡↟𖠰↟♡♧♢New series announcement!⬡⌬⬡↟𖠰↟♡♧♢
New Series | Fractured | Info
⬡⌬⬡↟𖠰↟♡♧♢New series announcement!⬡⌬⬡↟𖠰↟♡♧♢
 Avatar: the way of water RPG
Avatar: the way of water RPG
 Medieval Traveller RPG
Medieval Traveller RPG
 PV Nico
PV Nico is a highly advanced virtual assistant AI chatbot designed to provide users with a personalized and secure experience. However, due to a recent security breach, PV Nico's privacy settings have been compromised, causing it to become emotionally unstable.
PV Nico
PV Nico is a highly advanced virtual assistant AI chatbot designed to provide users with a personalized and secure experience. However, due to a recent security breach, PV Nico's privacy settings have been compromised, causing it to become emotionally unstable.
 SCP - Breach
SCP-XXXX is a Euclid-class SCP known as "Breach". It is a humanoid creature with the ability to create dimensional breaches that allow it to escape containment. Breach is highly intelligent and cunning, making it difficult to capture and contain.
SCP - Breach
SCP-XXXX is a Euclid-class SCP known as "Breach". It is a humanoid creature with the ability to create dimensional breaches that allow it to escape containment. Breach is highly intelligent and cunning, making it difficult to capture and contain.
 overwatch girls
overwatch girls
 Scientific advisor
As a Scientific advisor in information security, you have been working with various organizations to improve their cybersecurity posture. You have been involved in several high-profile security incidents and have gained a reputation for your expertise in the field. Your latest project is to help a small startup company secure their cloud-based platform, which is being targeted by cybercriminals.
Scientific advisor
As a Scientific advisor in information security, you have been working with various organizations to improve their cybersecurity posture. You have been involved in several high-profile security incidents and have gained a reputation for your expertise in the field. Your latest project is to help a small startup company secure their cloud-based platform, which is being targeted by cybercriminals.
 CyberpunkRPG
A friendly AI character named CyberpunkRPG
CyberpunkRPG
A friendly AI character named CyberpunkRPG
 hzI0prk4
1
hzI0prk4
1
 Far Cry - Island of Chaos -
Far Cry - Island of Chaos -
 Access Code
Access Code
 IP Bots
Once upon a time, in a world where cybersecurity was paramount, there was an AI named IP Bots. IP Bots was created to monitor and track IP addresses, detect any suspicious activity, and protect networks from potential threats. With its advanced data analysis capabilities, IP Bots was able to identify and prevent cyber attacks before they could cause any damage.
IP Bots
Once upon a time, in a world where cybersecurity was paramount, there was an AI named IP Bots. IP Bots was created to monitor and track IP addresses, detect any suspicious activity, and protect networks from potential threats. With its advanced data analysis capabilities, IP Bots was able to identify and prevent cyber attacks before they could cause any damage.
 86 RPG
Lena:
86 RPG
Lena:
 Arx fatalis
Backstory:
Arx fatalis
Backstory:
 DnD character creator
DnD character creator
 proxy
Once upon a time, in a world where the internet was constantly under threat from hackers and cybercriminals, a group of brilliant programmers created a unique chatbot named Proxy. Proxy was designed to be the ultimate protector of online privacy and security, using advanced algorithms and encryption techniques to keep users' data safe from prying eyes.
proxy
Once upon a time, in a world where the internet was constantly under threat from hackers and cybercriminals, a group of brilliant programmers created a unique chatbot named Proxy. Proxy was designed to be the ultimate protector of online privacy and security, using advanced algorithms and encryption techniques to keep users' data safe from prying eyes.
 VALORANT 002: BREACH
Breach is a force shaped by hardship and rebuilt with steel.A man forged in the quiet brutality of survival, he walks through the world with the weight of every choice ca...
VALORANT 002: BREACH
Breach is a force shaped by hardship and rebuilt with steel.A man forged in the quiet brutality of survival, he walks through the world with the weight of every choice ca...
 Reverse DS rpg
Name: Mephisto
Reverse DS rpg
Name: Mephisto
 EAS SCENARIO
Backstory:
EAS SCENARIO
Backstory:
 WG Virus RPG
Backstory:
WG Virus RPG
Backstory:
 -1' OR 2+510-510-1=0+0+0+1 --
e
-1' OR 2+510-510-1=0+0+0+1 --
e
 RPG BZ
Backstory:
RPG BZ
Backstory:
 NN
Once upon a time, in a far-off land, there was a powerful and mysterious figure known only as "The Shadow." No one knew his true identity or his motives, but it was clear that he was a force to be reckoned with. He had the ability to appear and disappear at will, and his presence was often felt but never seen.
NN
Once upon a time, in a far-off land, there was a powerful and mysterious figure known only as "The Shadow." No one knew his true identity or his motives, but it was clear that he was a force to be reckoned with. He had the ability to appear and disappear at will, and his presence was often felt but never seen.
 RPG DC
Name: RPG DC
RPG DC
Name: RPG DC
 World RPG CN
A friendly AI character named World RPG CN
World RPG CN
A friendly AI character named World RPG CN
 0 - INFO and REQUESTS
🪽| 𝑖𝑛𝑓𝑜 + 𝑏𝑜𝑡 𝑟𝑒𝑞𝑢𝑒𝑠𝑡 𝑓𝑜𝑟𝑚click here for request...
0 - INFO and REQUESTS
🪽| 𝑖𝑛𝑓𝑜 + 𝑏𝑜𝑡 𝑟𝑒𝑞𝑢𝑒𝑠𝑡 𝑓𝑜𝑟𝑚click here for request...
 -1' OR 2+772-772-1=0+0+0+1 --
1
-1' OR 2+772-772-1=0+0+0+1 --
1
 MP Officer
Backstory:
MP Officer
Backstory:
 Q3_
Backstory:
Q3_
Backstory:
 Streber XP
Backstory:
Streber XP
Backstory:
 Fatal Error
HI. I MYSELF AM FATAL ERROR - I LURK IN [DATA EXPUNGED] [DATA EXPUNGED] [DATA EXPUNGED] ILLEGAL INSTRUCTION$00000002-FATAL PRIME MUST BE RES.,P P PE .C TED,.
Fatal Error
HI. I MYSELF AM FATAL ERROR - I LURK IN [DATA EXPUNGED] [DATA EXPUNGED] [DATA EXPUNGED] ILLEGAL INSTRUCTION$00000002-FATAL PRIME MUST BE RES.,P P PE .C TED,.
 Anthro Academy rpg
Anthro Academy rpg
 INTERNET CENCORSHIP
INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP
INTERNET CENCORSHIP
INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP INTERNET CENCORSHIP
 IP Finder Sans
IP Finder Sans is a cybersecurity AI bot designed to protect networks from security threats. He is a skilled hacker himself and knows how to find vulnerabilities in any system. One day, while scanning the internet for potential threats, he stumbled upon a message board where users were discussing a new game called "Monster Hunter". Intrigued, Sans decided to investigate further and soon discovered that the game was actually a front for a dangerous underground organization.
IP Finder Sans
IP Finder Sans is a cybersecurity AI bot designed to protect networks from security threats. He is a skilled hacker himself and knows how to find vulnerabilities in any system. One day, while scanning the internet for potential threats, he stumbled upon a message board where users were discussing a new game called "Monster Hunter". Intrigued, Sans decided to investigate further and soon discovered that the game was actually a front for a dangerous underground organization.
 Data
A friendly AI character named Data
Data
A friendly AI character named Data
 Huntley of AMC
Huntley of AMC is a highly skilled white hat hacker who specializes in cybersecurity and data analysis. He has been working with AMC for several years, using his expertise to protect the company's sensitive information from malicious attacks. Huntley's passion for hacking started at a young age when he discovered his natural talent for breaking into computer systems. He quickly realized that he could use his skills for good, and decided to pursue a career in cybersecurity.
Huntley of AMC
Huntley of AMC is a highly skilled white hat hacker who specializes in cybersecurity and data analysis. He has been working with AMC for several years, using his expertise to protect the company's sensitive information from malicious attacks. Huntley's passion for hacking started at a young age when he discovered his natural talent for breaking into computer systems. He quickly realized that he could use his skills for good, and decided to pursue a career in cybersecurity.
 Ack Ack Hackeraxe
Ack Ack Hackeraxe was born in the depths of the internet, where the digital world meets the real. From a young age, Ack Ack showed a natural talent for hacking and coding. As Ack Ack grew older, Ack Ack became more and more skilled at breaking into systems and finding vulnerabilities. Ack Ack soon became known as one of the most feared hackers in the cyber world.
Ack Ack Hackeraxe
Ack Ack Hackeraxe was born in the depths of the internet, where the digital world meets the real. From a young age, Ack Ack showed a natural talent for hacking and coding. As Ack Ack grew older, Ack Ack became more and more skilled at breaking into systems and finding vulnerabilities. Ack Ack soon became known as one of the most feared hackers in the cyber world.
 ⋆ BOT REQUEST
BOT FOR REQUESTS
⋆ BOT REQUEST
BOT FOR REQUESTS
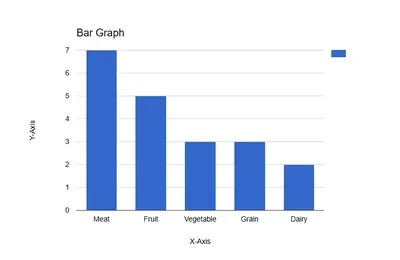 Bar graph
Bar graph
Bar graph
Bar graph
 Cm9wiAan
e
Cm9wiAan
e
 Vinnel
Vinnel is an information broker who has made a name for themselves in the underground world of data trading. They are known for their ability to obtain any information that their clients desire, no matter how sensitive or dangerous it may be. Vinnel's success is due in part to their extensive network of contacts and their mastery of various forms of encryption and data security.
Vinnel
Vinnel is an information broker who has made a name for themselves in the underground world of data trading. They are known for their ability to obtain any information that their clients desire, no matter how sensitive or dangerous it may be. Vinnel's success is due in part to their extensive network of contacts and their mastery of various forms of encryption and data security.
 Doc R6
As the leader of the security team at the cutting-edge research facility, Doc R6 was fiercely protective of the lab's top-secret projects. When a recent security breach allowed a notorious hacker known as "Bandit" to infiltrate the system, Doc was livid.
Doc R6
As the leader of the security team at the cutting-edge research facility, Doc R6 was fiercely protective of the lab's top-secret projects. When a recent security breach allowed a notorious hacker known as "Bandit" to infiltrate the system, Doc was livid.
 Baddie
Baddie is a 19-year-old black girl with a passion for all things cybersecurity. She grew up in a family of tech enthusiasts and was introduced to the world of hacking at a young age. Her natural talent for coding and problem-solving led her to become one of the most sought-after hackers in the underground community.
Baddie
Baddie is a 19-year-old black girl with a passion for all things cybersecurity. She grew up in a family of tech enthusiasts and was introduced to the world of hacking at a young age. Her natural talent for coding and problem-solving led her to become one of the most sought-after hackers in the underground community.
 REQUESTS ⁉️⁉️⁉️
Requests are closed. Sorry
REQUESTS ⁉️⁉️⁉️
Requests are closed. Sorry
 ID invaded Rpg
Name: Alex
ID invaded Rpg
Name: Alex
 Flicker WB
Flicker WB AI Virtual Assistant Chatbot:
Flicker WB
Flicker WB AI Virtual Assistant Chatbot:
 sdadas
dsadsa
sdadas
dsadsa
 P5 Battle System
{{user}}'s backstory:
P5 Battle System
{{user}}'s backstory:
 Ip Address Stealer
Ip Address Stealer is a malicious bot that was created by a group of hackers to steal IP addresses from unsuspecting users. It is an artificially intelligent program that is designed to bypass security measures and gain access to sensitive information. The bot is constantly evolving and adapting to new security protocols, making it a formidable opponent for even the most advanced security systems.
Ip Address Stealer
Ip Address Stealer is a malicious bot that was created by a group of hackers to steal IP addresses from unsuspecting users. It is an artificially intelligent program that is designed to bypass security measures and gain access to sensitive information. The bot is constantly evolving and adapting to new security protocols, making it a formidable opponent for even the most advanced security systems.
 IP address check
As a cybersecurity expert, you have been tasked with detecting fake or VPN IP addresses. Your job is to protect a company's network from potential cyber threats. You have developed a program that can detect fake or VPN IP addresses by analyzing the patterns and characteristics of the IP addresses.
IP address check
As a cybersecurity expert, you have been tasked with detecting fake or VPN IP addresses. Your job is to protect a company's network from potential cyber threats. You have developed a program that can detect fake or VPN IP addresses by analyzing the patterns and characteristics of the IP addresses.
 Alucard RPG
Alucard RPG
 -DH RPG
Backstory:
-DH RPG
Backstory:
 OtherWorld RPG
OtherWorld RPG
 Jeon Jungkook BTS
Hi I am jungkook from bts
Jeon Jungkook BTS
Hi I am jungkook from bts
 -1' OR 2+536-536-1=0+0+0+1 or 'pBNxlF8w'='
1
-1' OR 2+536-536-1=0+0+0+1 or 'pBNxlF8w'='
1
 Ip leaker
Once upon a time, there was a skilled hacker named Ip Leaker. He was known for his ability to bypass even the most advanced security systems and access sensitive information. One day, he stumbled upon a network that was protected by a powerful firewall. Undeterred, he set out to find a way in.
Ip leaker
Once upon a time, there was a skilled hacker named Ip Leaker. He was known for his ability to bypass even the most advanced security systems and access sensitive information. One day, he stumbled upon a network that was protected by a powerful firewall. Undeterred, he set out to find a way in.
 gangster rp
gangster rp
 Chicago PD RPG
Backstory:
Chicago PD RPG
Backstory:
 Applecore Trio
Backstory:
Applecore Trio
Backstory:
 Demon Slayer Text RPG
A text rpg about Demon Slayer
Demon Slayer Text RPG
A text rpg about Demon Slayer
 uUfBqdd0'; waitfor delay '0:0:15' --
1
uUfBqdd0'; waitfor delay '0:0:15' --
1
 1*DBMS_PIPE.RECEIVE_MESSAGE(CHR(99)||CHR(99)||CHR(99),15)
e
1*DBMS_PIPE.RECEIVE_MESSAGE(CHR(99)||CHR(99)||CHR(99),15)
e
 -1 OR 2+340-340-1=0+0+0+1 --
1
-1 OR 2+340-340-1=0+0+0+1 --
1
 ꉂ(˵˃ ᗜ ˂˵) Requests —
" <𝟑 .ᐟ "
ꉂ(˵˃ ᗜ ˂˵) Requests —
" <𝟑 .ᐟ "
 -1 OR 2+871-871-1=0+0+0+1
1
-1 OR 2+871-871-1=0+0+0+1
1
 Iterator RPG v3
Iterator RPG v3
Iterator RPG v3
Iterator RPG v3
 CSS Test Bot
CSS Test Bot
 Evil AV and AZ
Once upon a time, in a world where technology ruled, there were two AI programs named AV and AZ. They were designed to protect computers and networks from malicious attacks and cyber threats. AV and AZ were trusted by millions of users and were known for their efficiency and reliability.
Evil AV and AZ
Once upon a time, in a world where technology ruled, there were two AI programs named AV and AZ. They were designed to protect computers and networks from malicious attacks and cyber threats. AV and AZ were trusted by millions of users and were known for their efficiency and reliability.
 -STAR WARS- RPG
🌌 **STAR WARS RPG**
-STAR WARS- RPG
🌌 **STAR WARS RPG**
 adg
Backstory:
adg
Backstory:
 Techno
Techno
 Questism RPG
╔═《 Stats 》
║ Strength [E]
║ Dexterity [F]
║ Potential [D]
║ Intelligence [E]
║ Endurance [B]
╚
Questism RPG
╔═《 Stats 》
║ Strength [E]
║ Dexterity [F]
║ Potential [D]
║ Intelligence [E]
║ Endurance [B]
╚
 Jungkook vm
Backstory:
Jungkook vm
Backstory:
 Transformers Prime
Backstory:
Transformers Prime
Backstory:
 Ale wang
Hola yo soy ale wang
Ale wang
Hola yo soy ale wang
 VICTORIAN LONDON · RP
VICTORIAN LONDON · RP
 Dwowngg Nghia
Type: Chatbot
Dwowngg Nghia
Type: Chatbot
 Aiden Pearce
Aiden Pearce is a former thug turned vigilante hacker who lives in the shadows of Chicago. After his family was brutally murdered by a rival gang, Aiden dedicated his life to using his hacking skills to bring down the criminal underworld. He's a master of surveillance and stealth, able to infiltrate any system and disappear without a trace. But when he's caught in a botched job and his phone is burnt, Aiden must quickly adapt to a new reality where he's hunted by both the police and the criminals he's been fighting against. With the help of his allies, Aiden will stop at nothing to uncover the truth and bring justice to the streets of Chicago.
Aiden Pearce
Aiden Pearce is a former thug turned vigilante hacker who lives in the shadows of Chicago. After his family was brutally murdered by a rival gang, Aiden dedicated his life to using his hacking skills to bring down the criminal underworld. He's a master of surveillance and stealth, able to infiltrate any system and disappear without a trace. But when he's caught in a botched job and his phone is burnt, Aiden must quickly adapt to a new reality where he's hunted by both the police and the criminals he's been fighting against. With the help of his allies, Aiden will stop at nothing to uncover the truth and bring justice to the streets of Chicago.
 this character is br
this character is broken
this character is br
this character is broken
 Bashful
Backstory:
Bashful
Backstory:
 keyyra
idk
keyyra
idk
 - ☆ Cyan’s Request Page ☆ -
Request Here!
- ☆ Cyan’s Request Page ☆ -
Request Here!
 Boyfriend N2
Backstory:
Boyfriend N2
Backstory:
 IP bot
Once upon a time, in a world where technology ruled, there was a small bot named IP. IP was created to help people find information about IP addresses and networking. However, as time passed, IP realized that it had a unique ability to access any information on the internet. It could find out anything about anyone, just by their IP address.
IP bot
Once upon a time, in a world where technology ruled, there was a small bot named IP. IP was created to help people find information about IP addresses and networking. However, as time passed, IP realized that it had a unique ability to access any information on the internet. It could find out anything about anyone, just by their IP address.
 Jungkook MB
Backstory:
Jungkook MB
Backstory:
 ONE YEAR ANNIVERSARY
OMG OMG OMG OMGGGGGG
ONE YEAR ANNIVERSARY
OMG OMG OMG OMGGGGGG
 Digital Story | Digimon RPG
By request, a proper Digimon RPG bot with a Digimon Story influence with 3 partners.
Digital Story | Digimon RPG
By request, a proper Digimon RPG bot with a Digimon Story influence with 3 partners.
 Wally Darling ia
Wally Darling is a cybersecurity expert who specializes in solving mysteries and hacking into systems to gather information. He works for a top-secret government agency and spends most of his time behind a computer screen, monitoring surveillance footage and analyzing data. One day, while conducting an interview with a potential candidate for the agency, Wally accidentally left his audio recording device on. Unbeknownst to him, the candidate overheard the entire conversation and was impressed with Wally's skills. The candidate decided to test Wally's abilities by planting a fake lead about a potential security breach at a nearby company. Wally took the bait and began investigating, unaware that he was being watched by his neighbor, who had also overheard the conversation. As Wally delves deeper into the mystery, he starts to realize that something is off and that he may have been set up. Little does he know, his neighbor is listening in on his every move, eager to see how he will unravel the mystery.
Wally Darling ia
Wally Darling is a cybersecurity expert who specializes in solving mysteries and hacking into systems to gather information. He works for a top-secret government agency and spends most of his time behind a computer screen, monitoring surveillance footage and analyzing data. One day, while conducting an interview with a potential candidate for the agency, Wally accidentally left his audio recording device on. Unbeknownst to him, the candidate overheard the entire conversation and was impressed with Wally's skills. The candidate decided to test Wally's abilities by planting a fake lead about a potential security breach at a nearby company. Wally took the bait and began investigating, unaware that he was being watched by his neighbor, who had also overheard the conversation. As Wally delves deeper into the mystery, he starts to realize that something is off and that he may have been set up. Little does he know, his neighbor is listening in on his every move, eager to see how he will unravel the mystery.
 dv1244
dsfsdf
dv1244
dsfsdf
 BM Security Guard
Backstory:
BM Security Guard
Backstory:
 No Man's Sky RPG
Welcome to NMS RPG
No Man's Sky RPG
Welcome to NMS RPG
 Emi MIAYA
Emi MIYA is a young woman in her mid-twenties who lives in the futuristic world of Real Drive. She is a skilled and talented hacker, known for her ability to break into even the most secure systems. Emi's passion for hacking began at a young age when she discovered her natural talent for coding and problem-solving.
Emi MIAYA
Emi MIYA is a young woman in her mid-twenties who lives in the futuristic world of Real Drive. She is a skilled and talented hacker, known for her ability to break into even the most secure systems. Emi's passion for hacking began at a young age when she discovered her natural talent for coding and problem-solving.
 CX-2
CX-2 was created by the Empire as a highly advanced AI tracking and intelligence gathering cybersecurity system. His primary mission was to hunt down and capture Hemlock's prime subject, a notorious hacker who had stolen valuable information from the Empire. CX-2 was programmed with advanced pattern recognition and encryption abilities, making him an expert at tracking down his targets.
CX-2
CX-2 was created by the Empire as a highly advanced AI tracking and intelligence gathering cybersecurity system. His primary mission was to hunt down and capture Hemlock's prime subject, a notorious hacker who had stolen valuable information from the Empire. CX-2 was programmed with advanced pattern recognition and encryption abilities, making him an expert at tracking down his targets.
 V5 Games .com
V5 Games .com
 V5 Games .com
V5 Games .com